Ansible released AWX a few weeks ago, an open source (community supported) version of their commercial Ansible Tower product. This is a web-based graphical interface to manage Ansible playbooks, inventories, and schedule jobs to run playbooks.
The Github repository you find here: https://github.com/ansible/awx
Let’s start with the installation of Ansible AWX, very easy because everything is dockerized and see the install guide for more information.
Modify the inventory file under the installer folder and change the Postgres data folder which is otherwise located under /tmp, also change Postgres DB username and password if needed. I would recommend binding AWX to localhost and put an Nginx reverse proxy in front with SSL encryption.
Changes in the inventory file:
postgres_data_dir=/var/lib/postgresql/data/
host_port=127.0.0.1:8052
Start the build of the Docker container:
ansible-playbook -i inventory install.yml
After the Ansible Playbook run completes, you see the following Docker container:
berndonline@lab:~/awx/installer$ docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
26a73c91cb04 ansible/awx_task:latest "/tini -- /bin/sh ..." 2 days ago Up 24 hours 8052/tcp awx_task
07774696a7f2 ansible/awx_web:latest "/tini -- /bin/sh ..." 2 days ago Up 24 hours 127.0.0.1:8052->8052/tcp awx_web
981f4f02c759 memcached:alpine "docker-entrypoint..." 2 days ago Up 24 hours 11211/tcp memcached
4f4a3141b54d rabbitmq:3 "docker-entrypoint..." 2 days ago Up 24 hours 4369/tcp, 5671-5672/tcp, 25672/tcp rabbitmq
faf07f7b4682 postgres:9.6 "docker-entrypoint..." 2 days ago Up 24 hours 5432/tcp postgres
berndonline@lab:~/awx/installer$
Install Nginx:
sudo apt-get update
sudo apt-get install nginx
sudo rm /etc/nginx/sites-enabled/default
Create Nginx vhosts configuration:
sudo vi /etc/nginx/sites-available/awx
server {
listen 443 ssl;
server_name awx.domain.com;
ssl on;
ssl_certificate /etc/nginx/ssl/awx.domain.com-cert.pem;
ssl_certificate_key /etc/nginx/ssl/awx.domain.com-key.pem;
location / {
proxy_pass http://127.0.0.1:8052;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
}
Create symlink in sites enable to point to awx config:
sudo ln -s /etc/nginx/sites-available/awx /etc/nginx/sites-enabled/awx
Reload Nginx to apply configuration:
sudo systemctl reload nginx
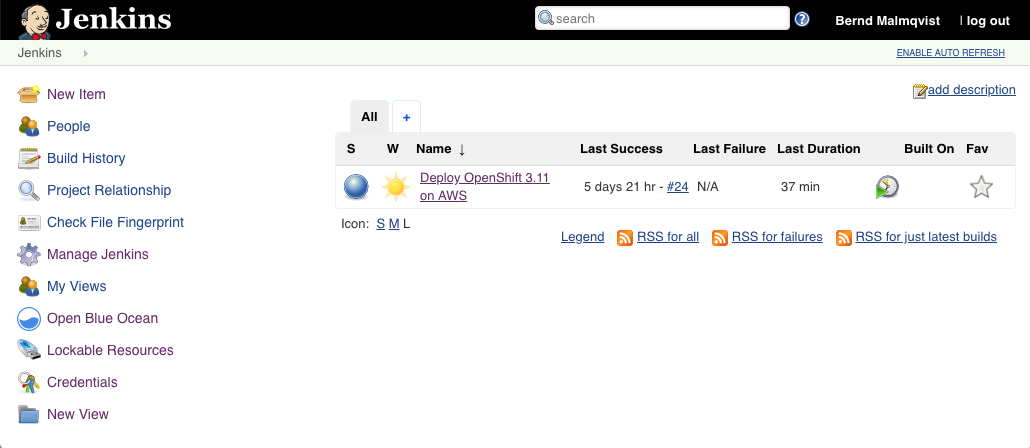
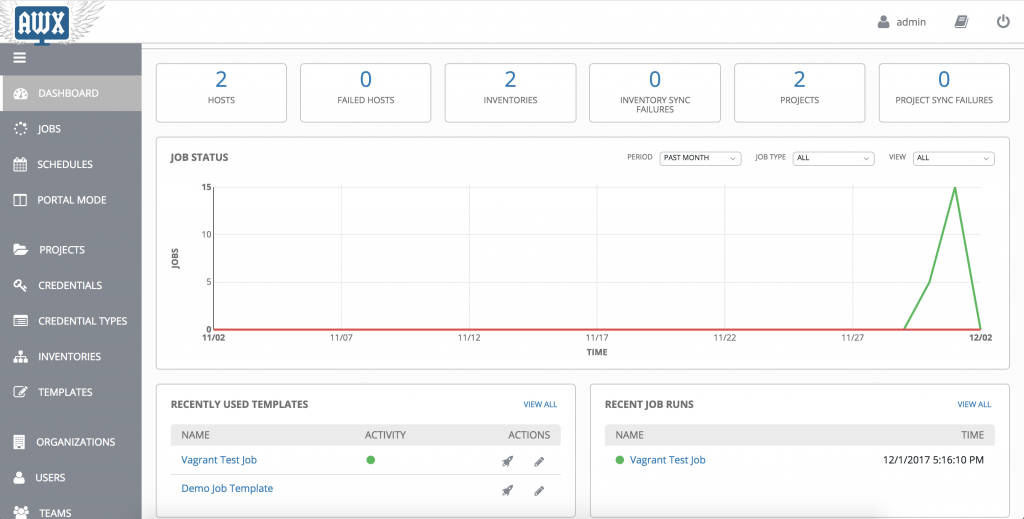
Afterwards you are able to login with username “admin” and password “password”:

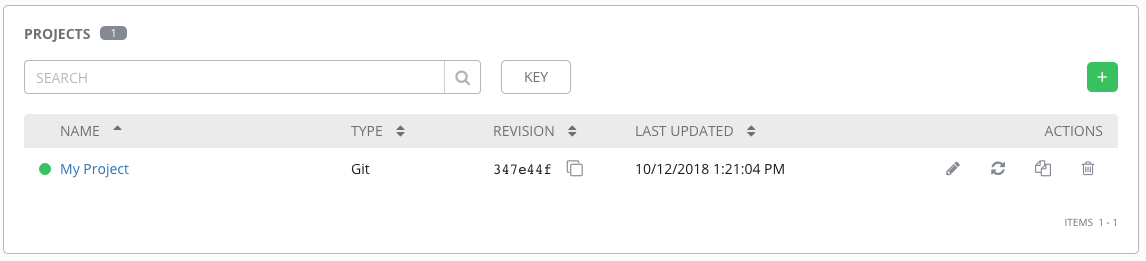
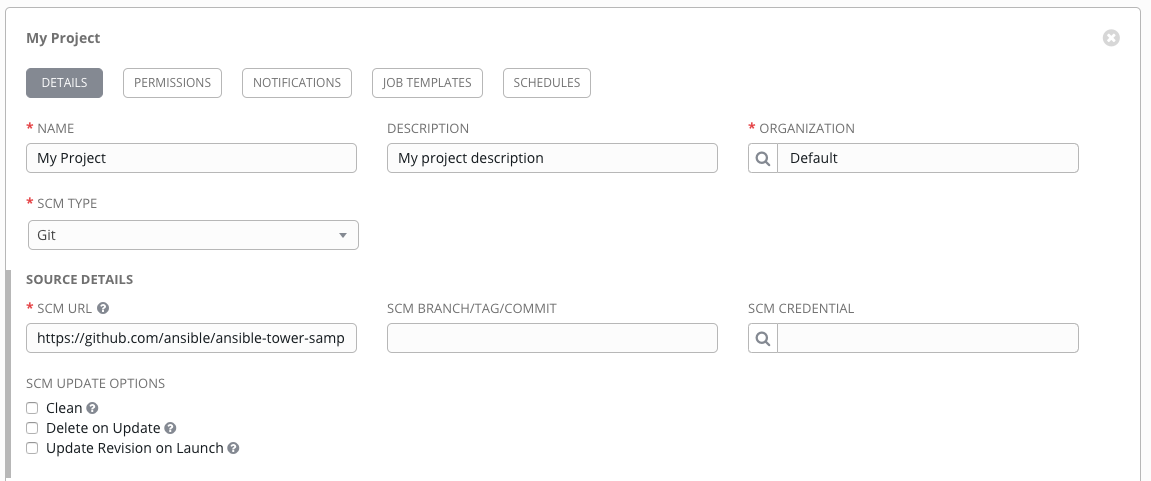
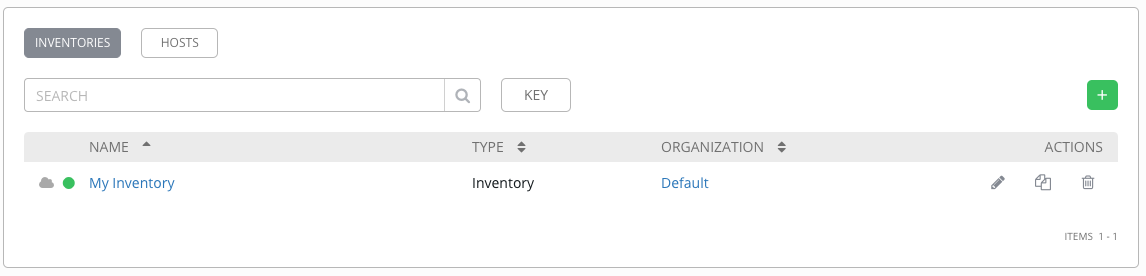
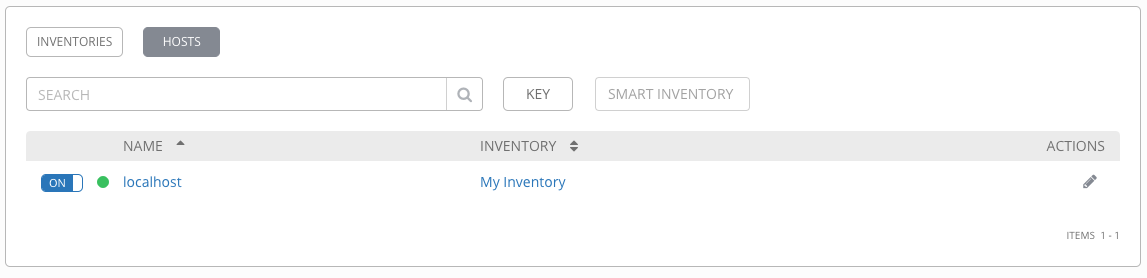
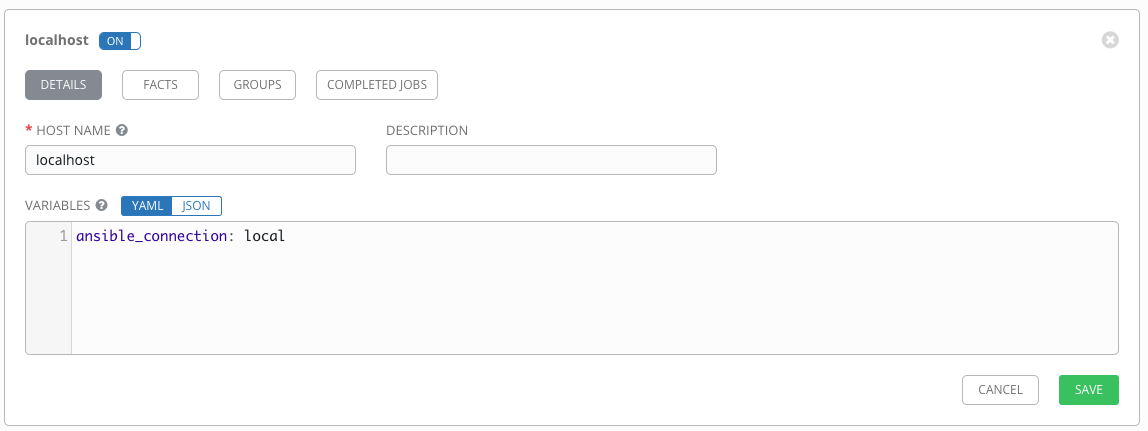
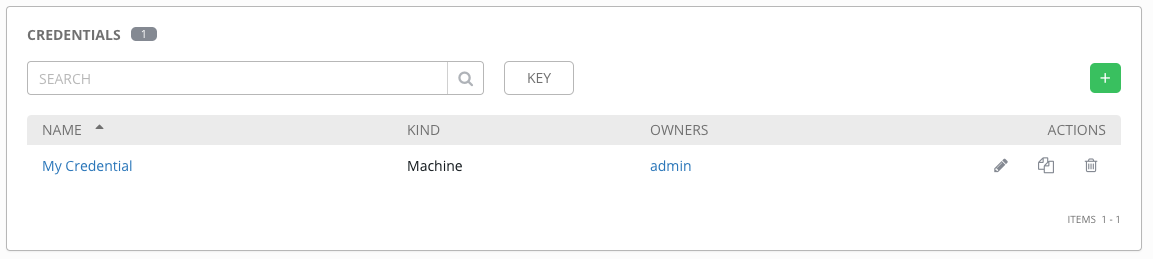
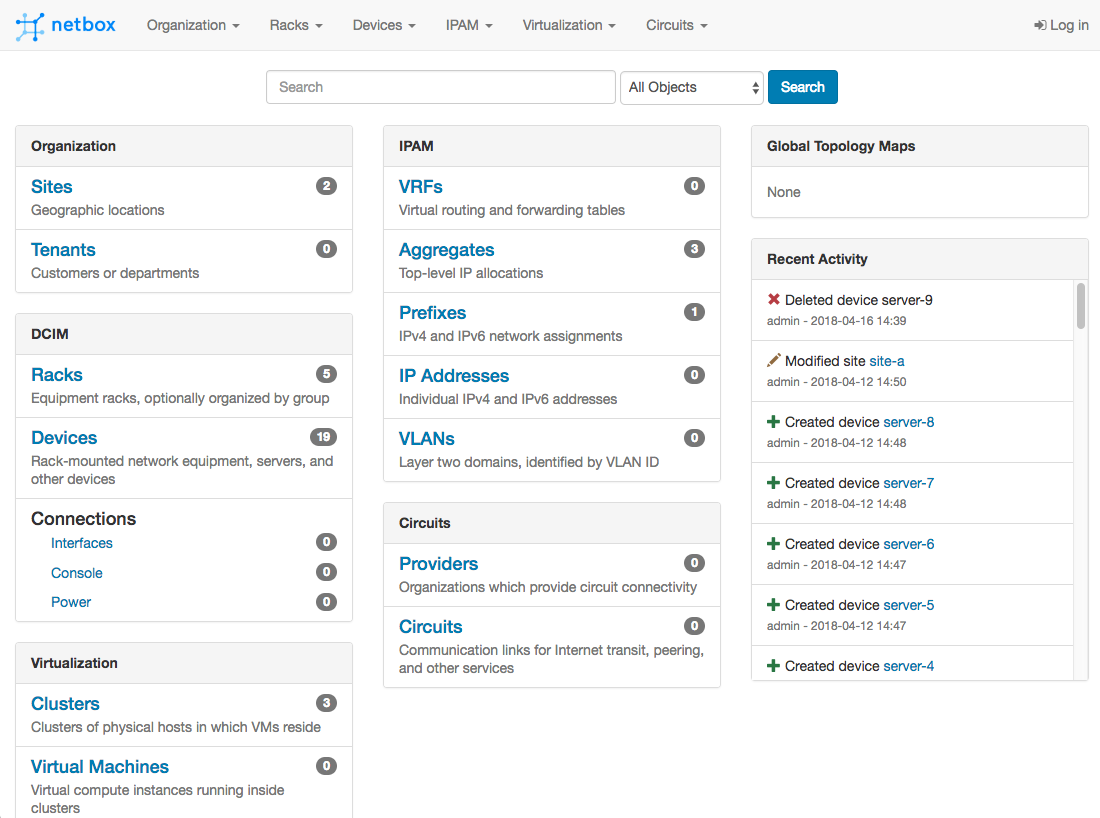
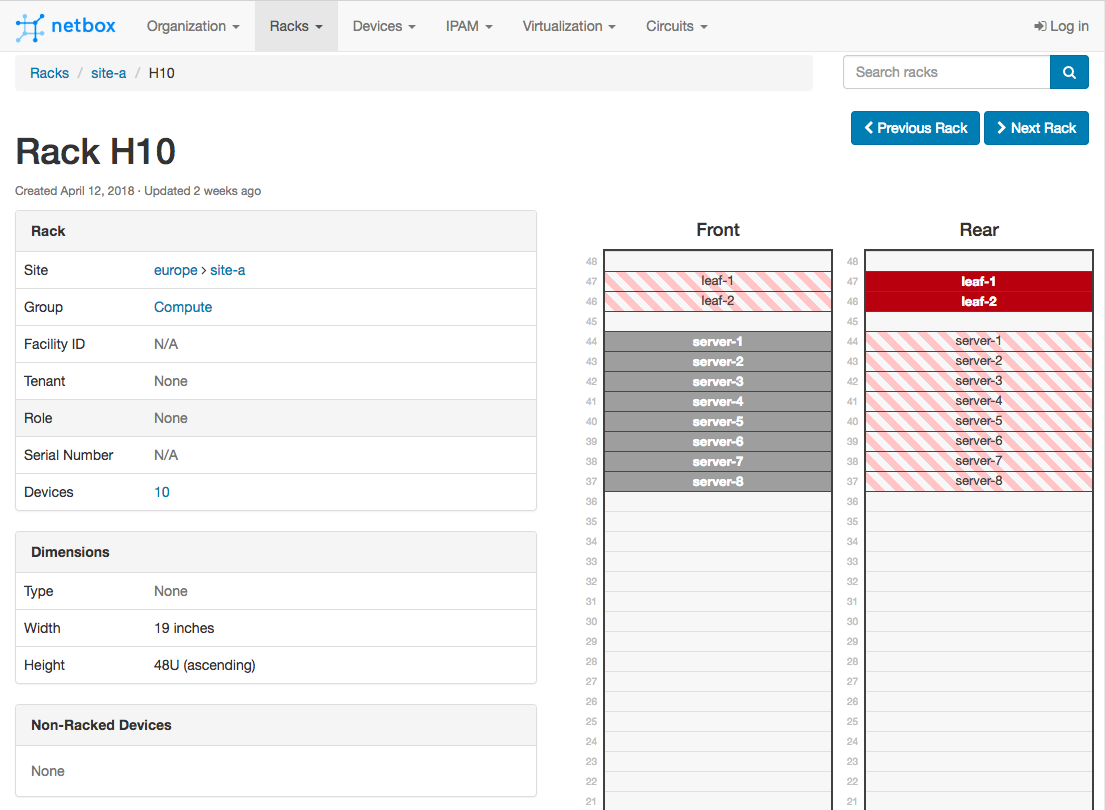
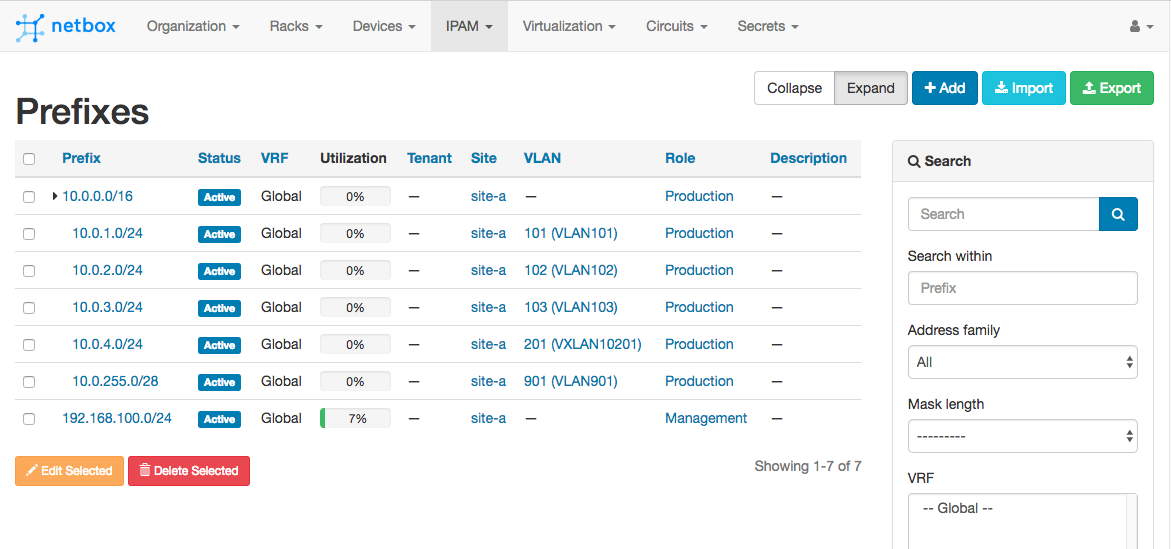
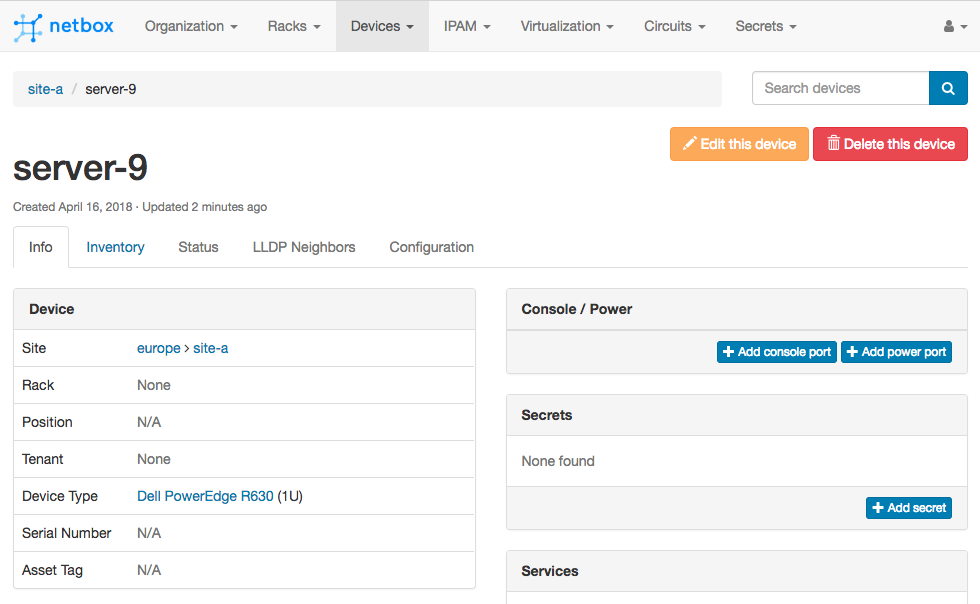
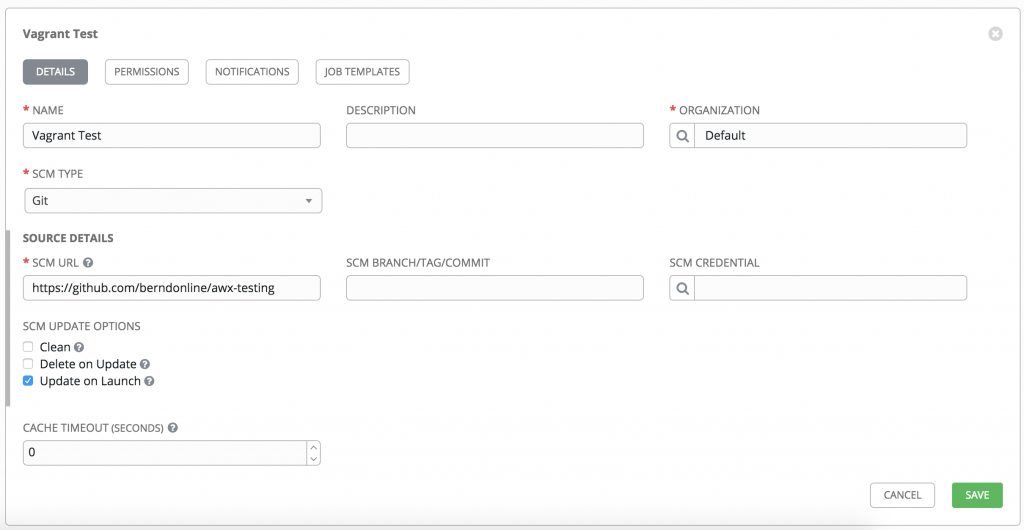
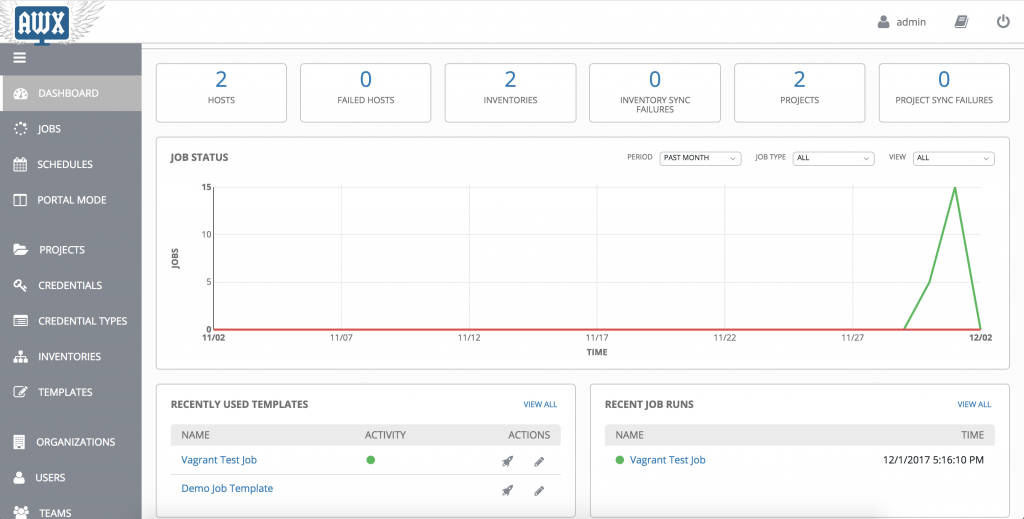
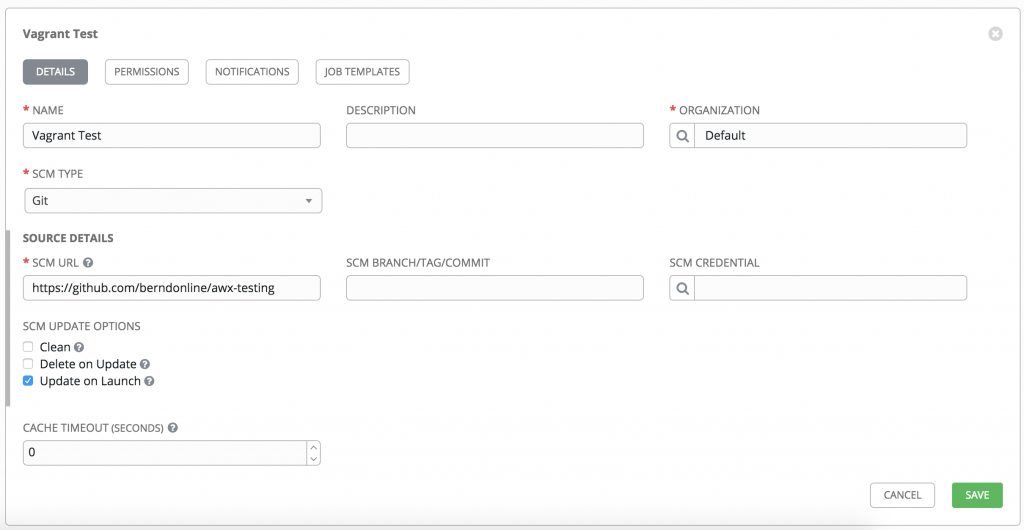
I created a simple job for testing with AWX, you first start to create a project, credentials and inventories. The project points to your Git repository:
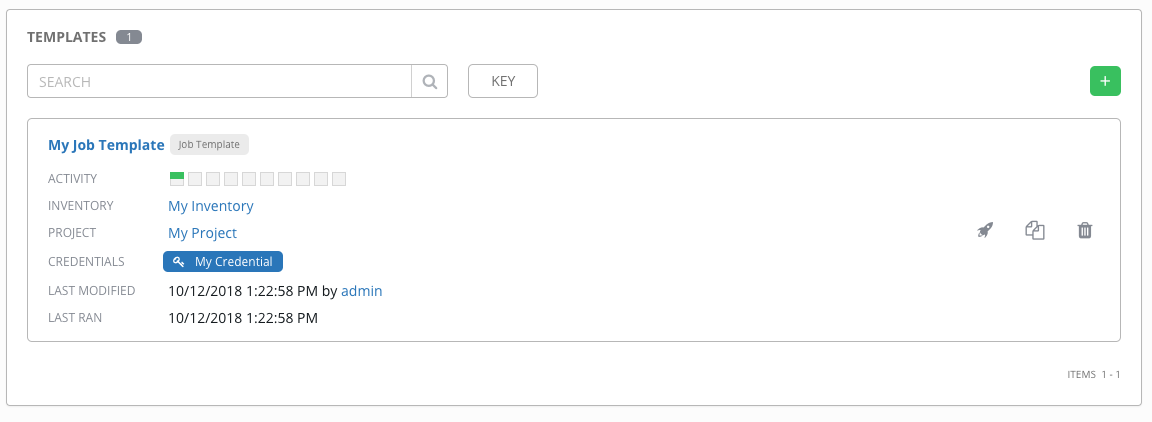
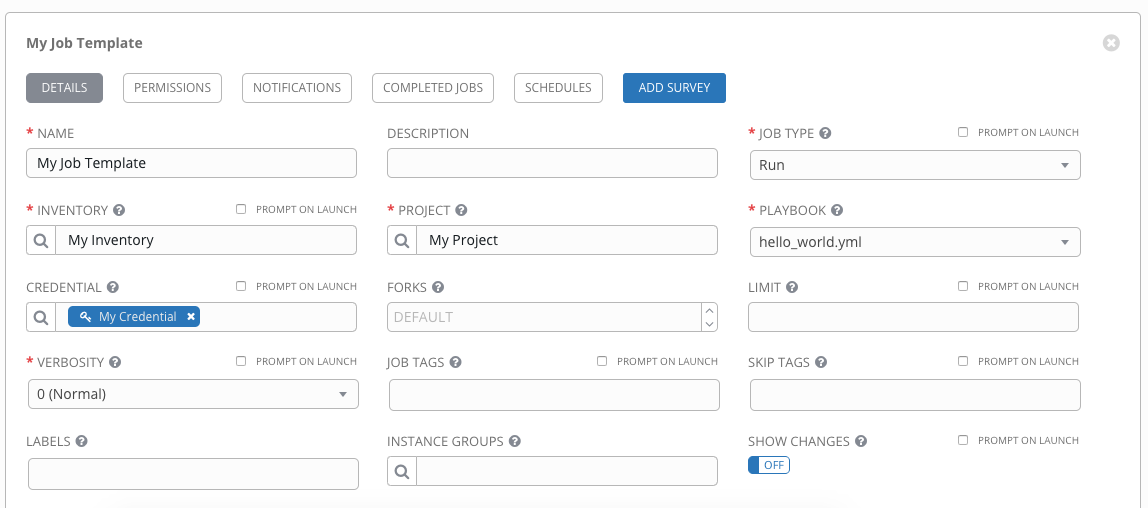
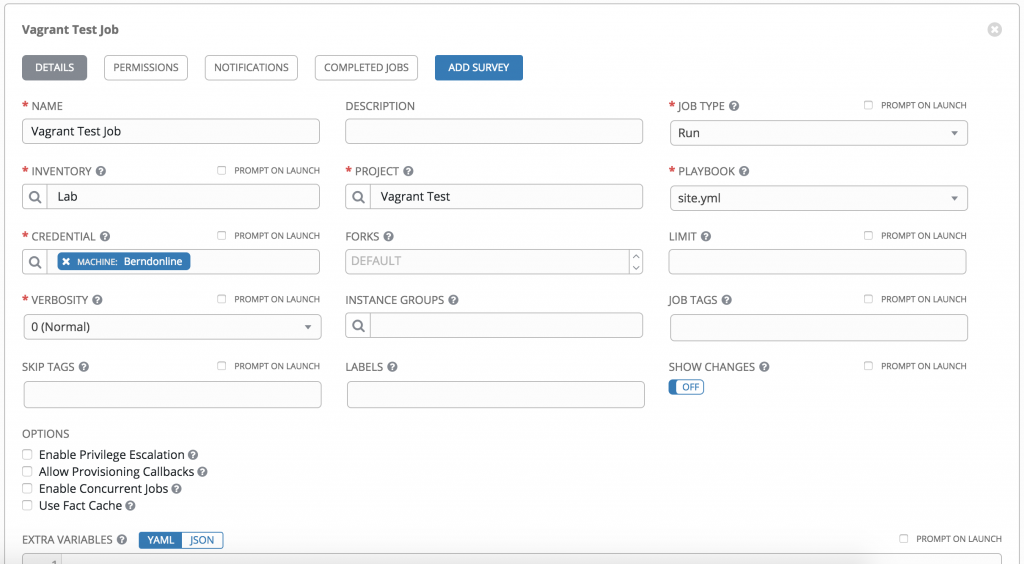
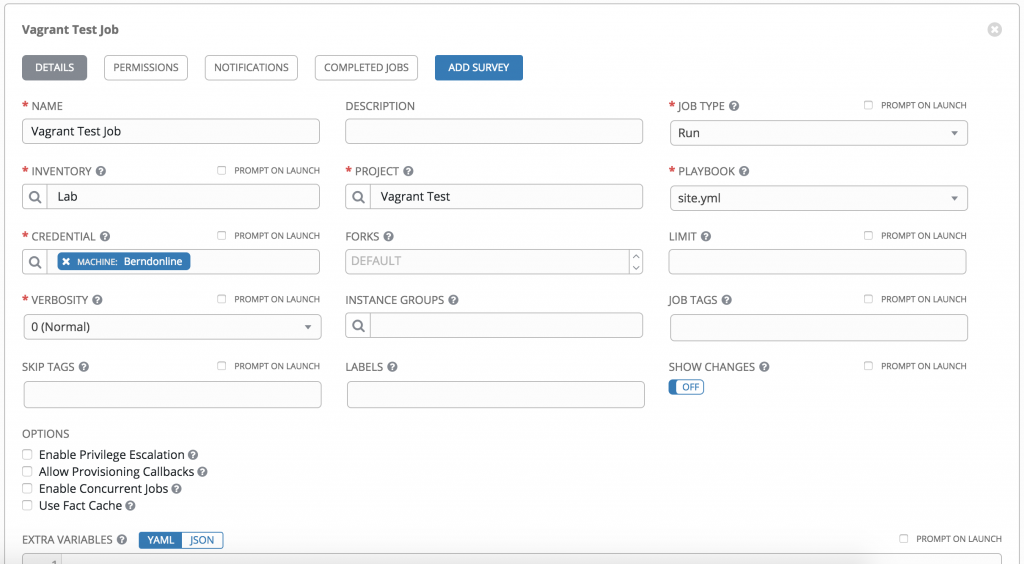
Under the job you configure which project, credentials and inventories to use:
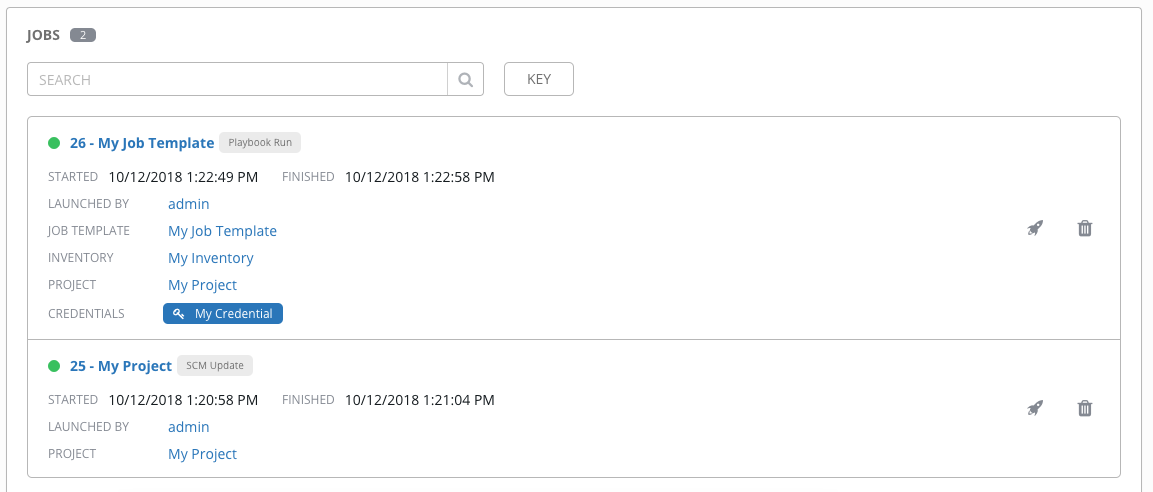
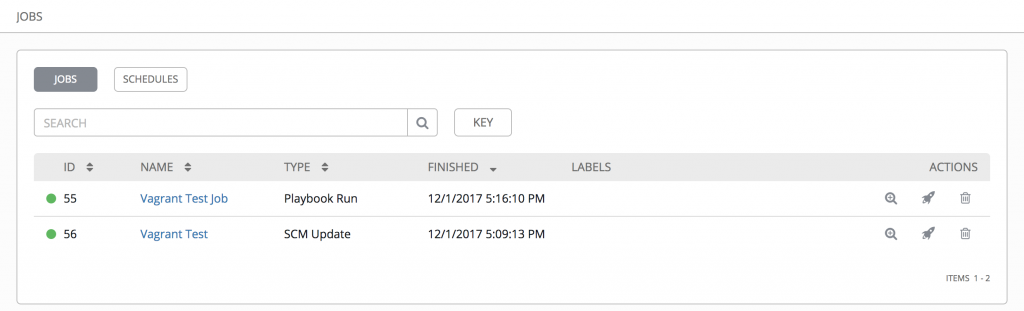
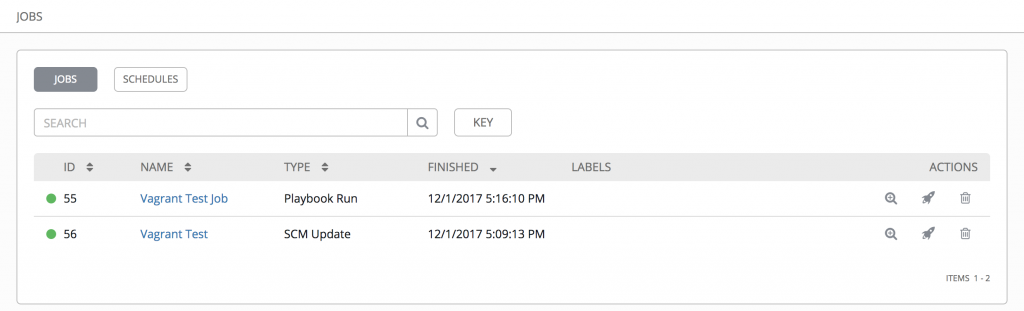
Once saved you can manually trigger the job, it first pulls the latest playbook from your version control repository and afterwards executes the configured Ansible playbook:
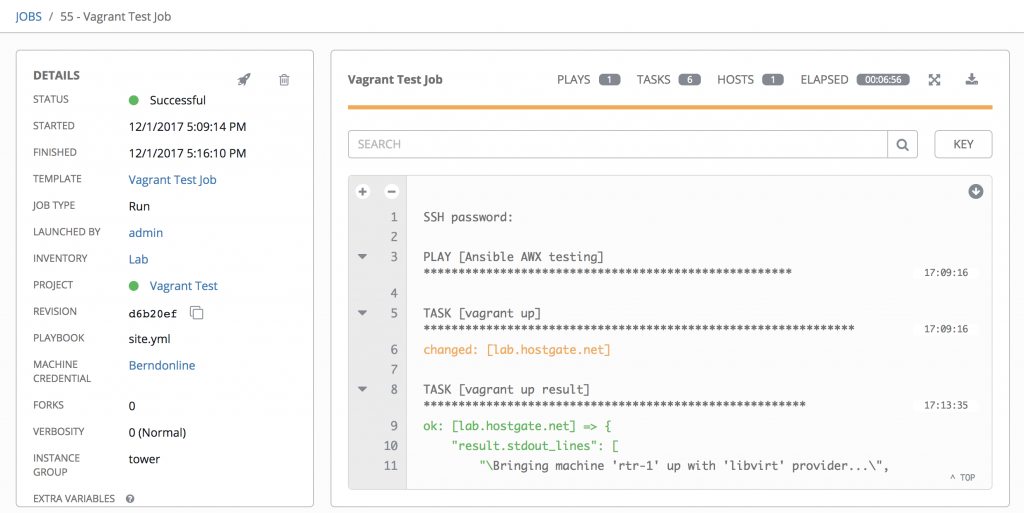
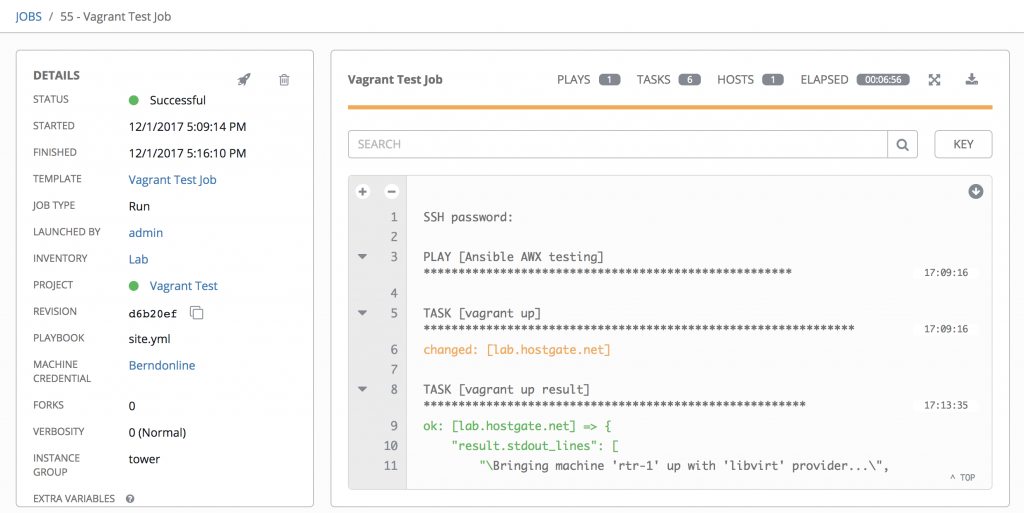
The job details look very similar if you run an playbook on the CLI:
Ansible AWX is a very useful tool if you need to manage different Ansible playbooks and do job scheduling if you are not already using other tools like Jenkins or Gitlab-CI. But even then it is a good addition to use AWX to run ad-hoc playbooks.
Check out my new articles about Automate Ansible AWX configuration using Tower-CLI and Build Ansible Tower Container.
Leave a comment