Here an Ansible Playbook with three different examples how to configure Cisco router interfaces:
1. Static IP address configuration in playbook
2. Configuration comes out of Jinja2 template, can be run dynamic with variables
3. Loop in playbook configures multiple interfaces
There are some disadvantages to work with templates, if you use commands like “no shutdown” to enable the interface. They are not shown in the running-configuration which means Ansible will assume that the configuration is not matching and execute the template again.
Another disadvantage with templates is that you cannot run “before” or “after” commands to remove existing configuration all this needs to be implemented in your Jinja2 template.
Here the Ansible Playbook:
- name: Cisco interface config
connection: local
hosts: all
gather_facts: false
vars:
cli:
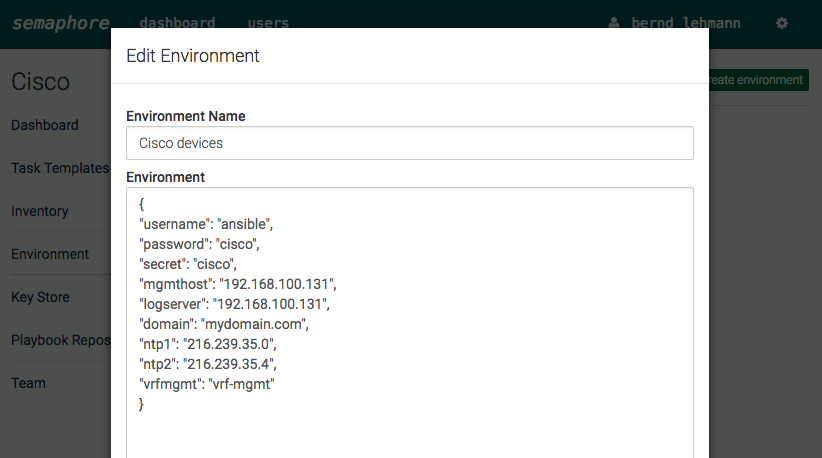
username: "{{ username }}"
password: "{{ password }}"
host: "{{ device_ip }}"
tasks:
- name: configure IP address
ios_config:
before:
- default interface FastEthernet1/0
lines:
- ip address 10.1.1.1 255.255.255.0
after:
- no shutdown
match: strict
parents: interface FastEthernet1/0
provider: "{{ cli }}"
- name: configure IP out of template
ios_config:
src: "interfaces.j2"
provider: "{{ cli }}"
- name: configure IP with loop
ios_config:
provider: "{{ cli }}"
before:
- "default interface {{ item.interface }}"
lines:
- "ip address {{ item.address }} 255.255.255.0"
after:
- no shutdown
parents: "interface {{ item.interface }}"
with_items:
- { interface : FastEthernet2/0, address : 10.3.3.3 }
- { interface : FastEthernet2/1, address : 10.4.4.4 }
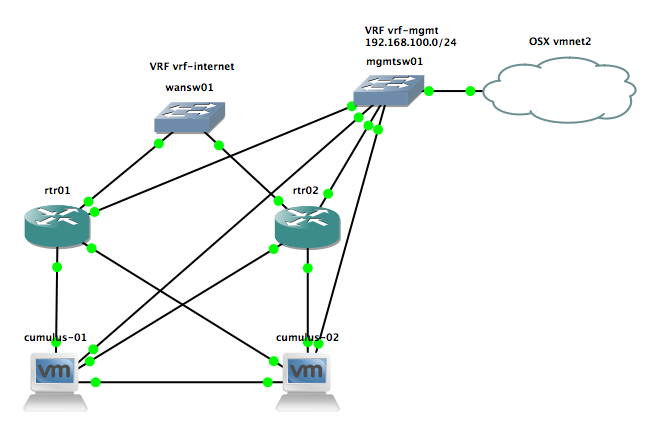
Read my new posts about Ansible Playbook for Cisco ASAv Firewall Topology or Ansible Playbook for Cisco BGP Routing Topology.